Introduction To
Vulnerability Assessment
Introduction To
Vulnerability Assessment
Creators: Dr. Steve Gosnell, Nate Adams, Jose Cintron, Chriss Koch
License: Creative Commons: Attribution, Share-Alike
(http://creativecommons.org/licenses/by-sa/3.0/)
Class Prerequisites: None
Lab Requirements:
- BackTrack Linux VM for familiarization
- Windows VM machine with WebGoat, Nessus, Nmap, Wireshark, and TamperData plugin for Firefox
- Various VM as targets (will be specified in more detail in the future)
Class Textbook: None
Recommended Class Duration: 3 days
Creators Available to Teach In-Person Classes: Yes
Author Comments:
This is a lecture and lab based class giving an introduction to vulnerability assessment of some common common computing technologies. Instructor-led lab exercises are used to demonstrate specific tools and technologies.
Course Objectives are
- Learning a general methodology for conducting assessments
- Scanning and mapping network topology
- Identifying listening ports/services on hosts
- Fingerprinting operating systems remotely
- Conducting automated vulnerability scans
- Auditing router, switch, and firewall security
- Auditing UNIX and Windows configuration and security
- Performing Web application and associated database security assessments
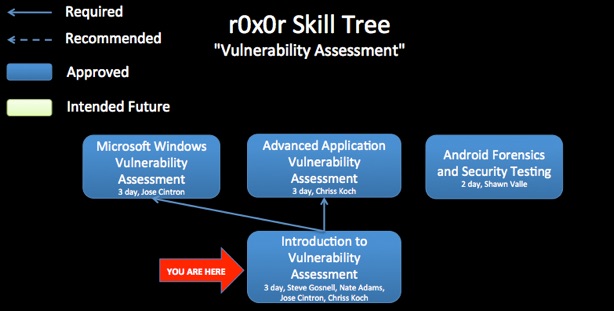
This class will serve as a prerequisite for later class on vulnerability assessment which dive deeper into specific areas such as Windows VA or web application VA.

Class Materials
(OpenOffice-formatted slides coming soon)

Revision History:
07-07-2012 - Initial class content upload
If you have used and modified this material, we would appreciate it if you submit your modified version for publishing here, so that all versions can benefit from your changes.