Exploits 2: Exploitation in the
Windows Environment
Creator: Corey Kallenberg @CoreyKal
License: Creative Commons: Attribution, Share-Alike
(http://creativecommons.org/licenses/by-sa/3.0/)
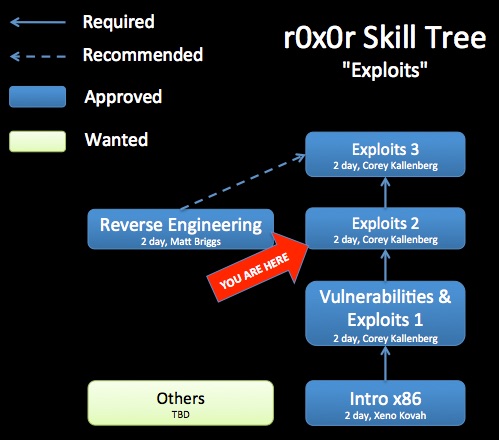
Class Prerequisites: Introduction to x86, Exploits 1
Lab Requirements:
Windows XP SP3 Virtual Machine with the following installed:
Windows Platform SDK 7.0 or 7.1 (optional debugging tools need to be installed)
Microsoft Visual C++ express 2008
HXD hex editor
Class Textbook: "The Shellcoder's Handbook: Discovering and Exploiting Security Holes" (2nd edition) by Chris Anley, John Heasman, Felix Lindner, Gerardo Richarte
Class Prereqs: Must have a basic understanding of the C programming language, as this class will show how C code can be exploited. Must have taken Intro x86 and Exploits 1. Some knowledge of the PE header format from Life of Binaries would be useful as well.
Recommended Class Duration: 3 days
Creator Available to Teach In-Person Classes: Yes
Author Comments:
This course covers the exploitation of stack corruption vulnerabilities in the Windows environment. Stack overflows are programming flaws that often times allow an attacker to execute arbitrary code in the context of a vulnerable program. There are many nuances involved with exploiting these vulnerabilities in Windows. Window's exploit mitigations such as DEP, ASLR, SafeSEH, and SEHOP, makes leveraging these programming bugs more difficult, but not impossible. The course highlights the features and weaknesses of many the exploit mitigation techniques deployed in Windows operating systems. Also covered are labs that describe the process of finding bugs in Windows applications with mutation based fuzzing, and then developing exploits that target those bugs.
Topics covered in the labs for this class include:
* Exploiting a vanilla Windows stack overflow with no mitigations turned on
* Using WinDbg to analyze our crashes
* Removing bytes from your payload (such as nulls) which would prevent exploitation
* Finding functions to call by walking the Thread Execution Block to find kernel32.dll’s location in memory so we can call functions like LoadLibrary() and GetProcAddress()
* Hashing strings to use for comparison when searching for functions, in order to minimize the size of the payload
* Overwriting Structured Exception Handlers (SEH) as a means to bypass stack cookies (/GS compile option) and bypassing the SafeSEH mitigation
* Overwriting virtual function table function pointers in C++ code as another way around stack cookies
* Using Return Oriented Programming (ROP) to defeat Data Execution Prevention (DEP) aka non-executable (NX) stack
* Using libraries which opt out of Address Space Layout Randomization (ASLR) and SafeSEH to bypass these mitigations
* Using Python to mutationally fuzz the custom, never-before-analyzed, Corey’s Crappy Document Format and Crappy Document Reader in order to find and exploit the numerous bugs within
Author Biography:
Corey Kallenberg co-founded LegbaCore in January 2015 to focus on improving firmware security. He has a Bachelors of Science in Computer Science from the University of Waterloo. His specialty areas are trusted computing, vulnerability research and low level development. In particular, Corey has spent several years using his vulnerability research expertise to evaluate limitations in current trusted computing implementations. In addition, he has used his development experience to create and improve upon trusted computing applications. Among these are a timing based attestation agent designed to improve firmware integrity reporting, and an open source Trusted Platform Module driver for Windows. Corey is also an experienced trainer, having created and delivered technical courses for the MITRE Institute, OpenSecurityTraining.info, CanSecWest, as well as numerous private customers. He is an internationally recognized speaker who has presented at BlackHat USA, DEF CON, CanSecWest, Hack in the Box KUL/AMS/GSEC, SummerCon, NoSuchCon, SyScan, EkoParty and Ruxcon. In 2015, Corey won the Pwnie award for best privilege escalation bug, for CERT VU# 552286, which exploits from userspace (ring 3) to SMM (ring “-2”), and which was found on hundreds of models of computers.

Class Materials
(.odp is best viewed with LibreOffice)
md5: 1ed93402bd2a2c0cc640a6308abb3222

Day 1 Part 1 (1:17:34, 1.08 GB)
Day 1 Part 2 (41:33, 804 MB)
Day 1 Part 3 (32:18, 635 MB)
Day 1 Part 4 (37:19, 645 MB)
Day 1 Part 5 (26:16, 493 MB)
Day 2 Part 1 (51:26, 575 MB)
Day 2 Part 2 (44:12, 568 MB)
Day 2 Part 3 (1:27:56, 696 MB)
Day 2 Part 4 (37:00, 472 MB)
Day 3 Part 1 (49:11, 583 MB)
Day 3 Part 2 (42:34, 569 MB)
Day 3 Part 3 (32:05, 696 MB)
Day 3 Part 4 (1:24:29, 472 MB)
(10:43:53 total, sans a lot of lab time)
The videos are useful for students, but also more useful for potential instructors who would like to teach this material. By watching the video, you will better understand the intent of some slides which do not stand on their own. You are recommended to watch the largest size video so that the most possible text is visible without having to follow along in the slides.

Revision History:
11-11-2012 - Day 3 videos uploaded to Youtube & Archive.org
09-30-2012 - Day 2 videos uploaded to Youtube & Archive.org
08-25-2012 - Day 1 videos uploaded to Youtube & Archive.org
08-25-2012 - Initial class content upload
If you have used and modified this material, we would appreciate it if you submit your modified version for publishing here, so that all versions can benefit from your changes.